Agentic Security
Zero Trust for AI Agents: Solving Identity and Access with AgentiD


Imagine giving every autonomous workflow in your company the same master credential to finance, support, and customer systems. That credential never expires, is reused everywhere, and is hard to revoke quickly without breaking production.
That pattern still exists in many agent deployments today.
AI agents are now operating across payment systems, ticketing systems, internal data stores, and SaaS control planes. But in too many environments, access control still relies on shared long-lived secrets designed for static services.
The result is predictable:
Broad access where narrow access is needed
Weak attribution when incidents happen
Slow revocation during active response
Difficult compliance evidence for delegated machine actions
This is not a future problem. It is an active operational risk.
The Real Problem: Agent Identity Does Not Map to Legacy IAM
Traditional IAM works well for humans and stable services. Autonomous agents have different characteristics:
They are often short-lived and task-scoped
They execute delegated actions on behalf of users or workflows
They may spawn hierarchies of child agents
They can perform high-volume API activity at machine speed
When these workloads are forced into a shared-service-account model, you lose two core security properties:
Precise identity at the workload instance level
Constrained capability at the operation level
Shared credential model
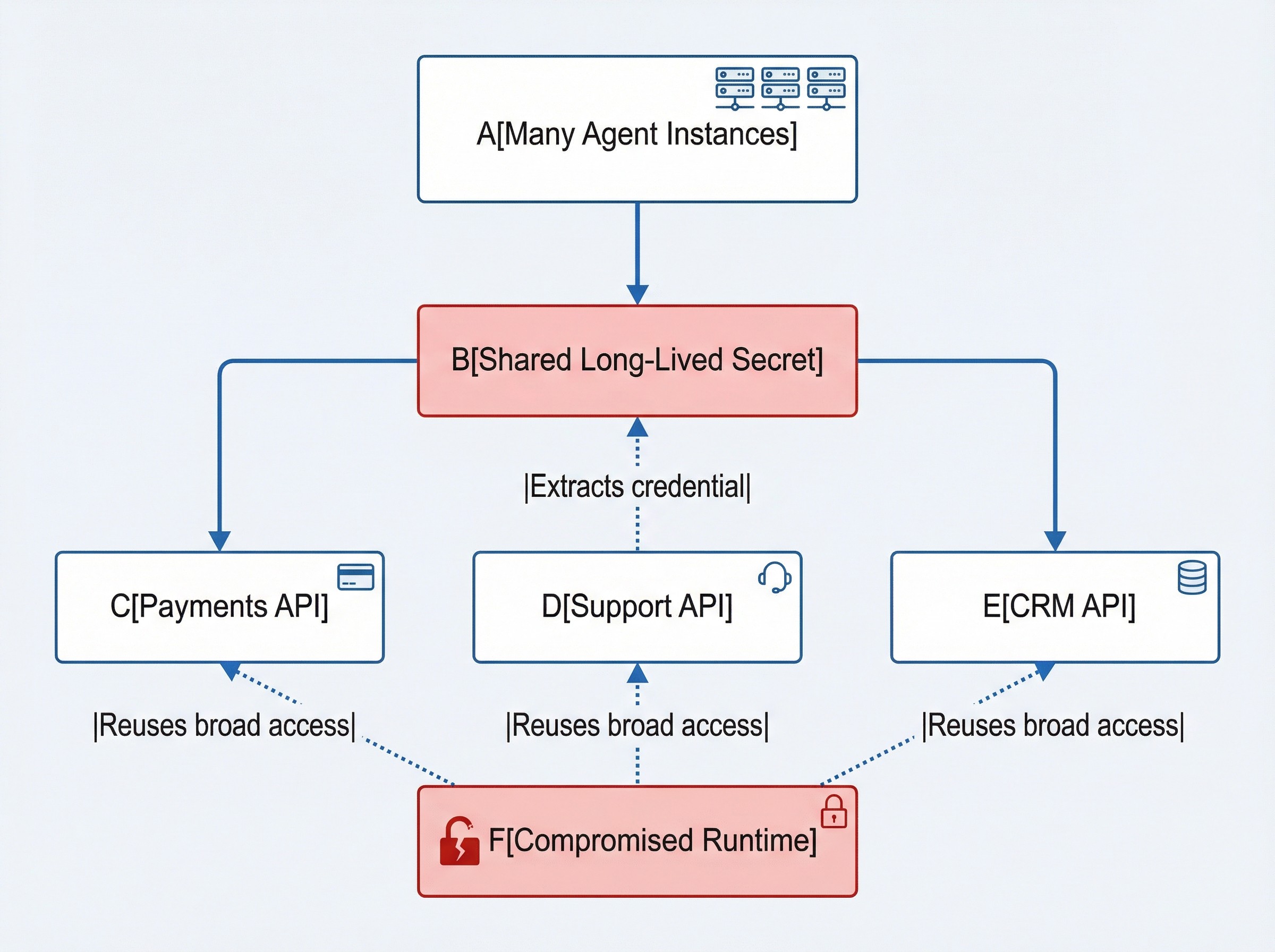
One compromise can create a disproportionate blast radius when identity and access boundaries are not workload-specific.
What Modern Agent Security Requires
A practical Zero Trust model for agents needs four foundations.
1. Short-Lived Access Tokens
Access should expire by default. Tokens that last minutes or hours dramatically reduce exposure compared with static secrets that persist for months.
2. Capability-Scoped Authorization
Tokens should contain explicit capabilities:
Resource target
Allowed scopes
Optional constraints (for example, transaction limits)
Expiry and identity context
3. Workload and Delegation Context
Security teams need to answer:
Which agent instance performed the action?
Under which delegated principal?
Under which tenant and policy context?
4. Continuous Runtime Enforcement
Authorization cannot be a one-time check at token issuance. Enforcement must continue at request time with runtime context, rate controls, and connector-level validation.
AgentID: Identity and Access Built for Agents
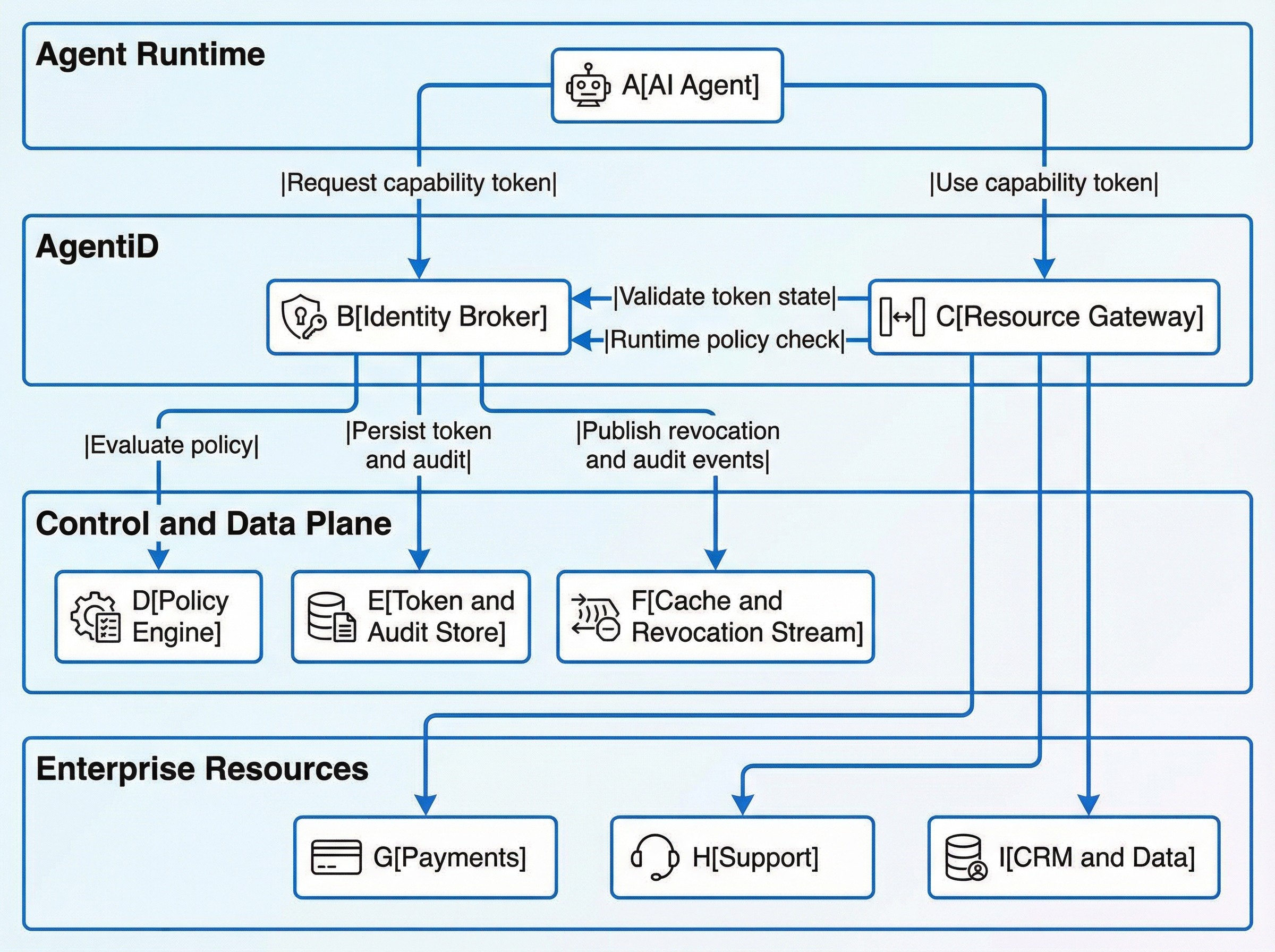
AgentID applies Zero Trust principles to autonomous systems with a two-plane architecture:
Identity Broker handles identity verification, policy evaluation, token issuance, introspection, revocation, and audit
Resource Gateway handles runtime validation, policy checks, rate limiting, and connector enforcement before downstream calls
High-level architecture
How Access Decisions Happen in Practice
Token issuance flow
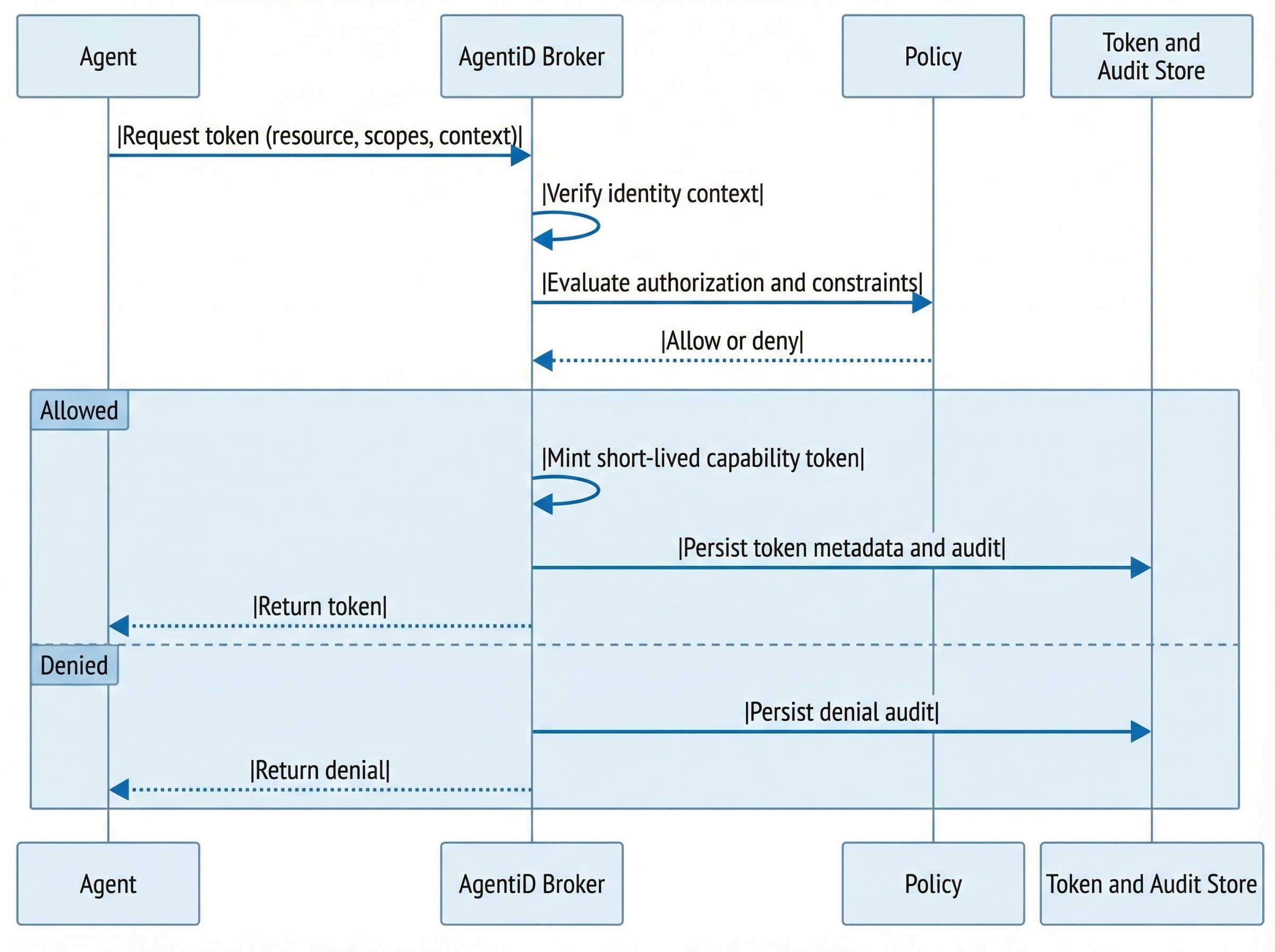
Runtime enforcement flow
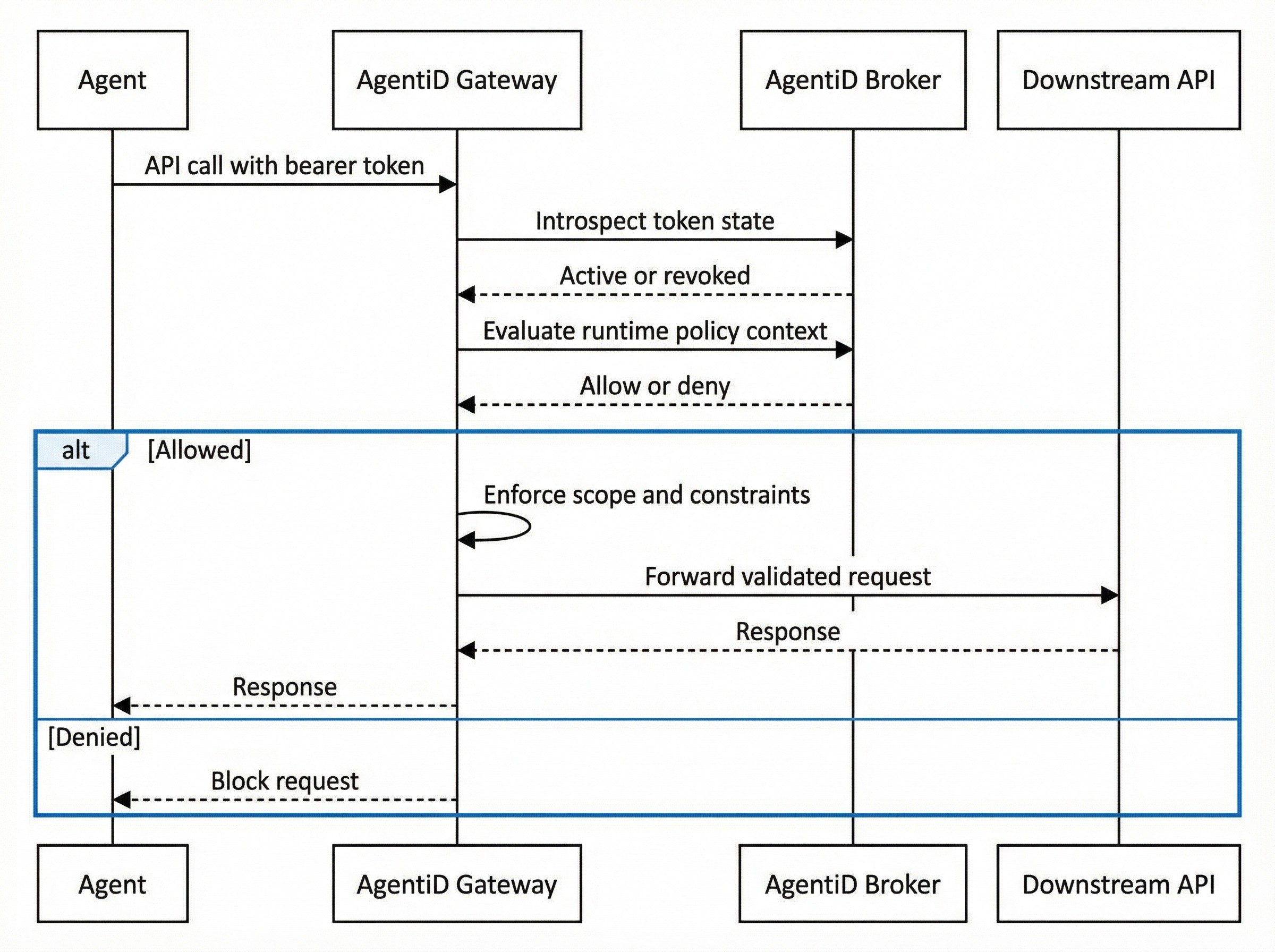
This model turns authorization into continuous verification rather than one-time trust.
Worked Example: Agent-Initiated Refund
Consider a customer support agent that needs to issue a refund. Without AgentID, this agent typically authenticates with a shared service account that has broad access to the payments API: read transactions, issue refunds, modify subscriptions, update billing details. A compromised runtime can reuse that credential for any of those operations.
With AgentID, the flow looks different:
The agent requests a capability token from the Broker scoped to
payments:refunda specific customer, with a constraint limiting the refund amount to the original transaction value.The Broker verifies the agent's identity, evaluates the tenant policy (refund agents may only issue refunds, not modify subscriptions), and mints a token that expires in five minutes.
The agent presents the token to the Gateway, which validates it, confirms the refund amount falls within the constraint, and forwards the request to the payments API.
After the refund completes, the token expires. The agent cannot reuse it, and a full audit trail links the refund to the specific agent instance, the delegated principal, and the policy that authorized it.
If the agent runtime is compromised during that window, the attacker holds a token that can only issue one bounded refund for one customer, expiring in minutes. Compare that with a shared credential that can modify any billing record indefinitely.
What Is Enforced at the Gateway
AgentiD gateway enforcement is designed for runtime safety, not just pass-through routing.
At request time, it can enforce:
Token activity and revocation status
Runtime policy decisions using request context
Scope checks per operation
Constraint checks per connector
Rate controls at the token and agent levels
Connector-based integrations support common enterprise systems, including payments, ticketing, collaboration, source control, secrets, cloud identity, and data access surfaces.
Design Principles Behind AgentID
Principle 1: Least Privilege Should Be Default
Every token should carry only what is required for the task, not a broad service-wide permission set.
Principle 2: Identity Must Be Explainable
Security and audit teams need clear machine-action lineage across tenant, principal, agent, and operation.
Principle 3: Revocation Must Be Operationally Fast
During incidents, revocation should propagate quickly to enforcement points without waiting for long token-cache windows.
Principle 4: Security Should Integrate, Not Rewrite
Teams should be able to adopt this model incrementally without replacing entire application stacks.
Recommended Adoption Path
A practical rollout usually follows this sequence:
Start with capability token issuance and introspection
Add runtime enforcement through the gateway
Enable federated identity for delegated enterprise principals
Adopt spawn-time agent lifecycle and delegation lineage controls
Expand connector constraints for high-risk workflows
This phased path reduces deployment risk while delivering immediate security improvements.
Why Not Just Use Existing Infrastructure?
A fair question. Cloud providers offer workload identity federation, and SPIFFE/SPIRE provides a mature framework for service identity attestation. Both are valuable, and AgentiD is designed to complement them, not replace them.
The gap is specificity. Cloud workload identity solves "which service is calling?" but not "which agent instance, acting under which delegated user, with which scoped capability, under which tenant policy?" SPIFFE gives you a verifiable identity document, but it does not mint capability-scoped tokens with runtime constraints, enforce per-operation policies at a gateway, or maintain delegation lineage across agent hierarchies.
AgentiD sits above the attestation layer. It can consume SPIFFE IDs or cloud workload tokens as identity inputs, then layer on the capability scoping, policy evaluation, delegation context, and runtime enforcement that agent workloads require. Think of it as the authorization and governance layer that identity attestation alone does not provide.
The Full Picture: Mirror Security's AI Security Platform
AgentID does not exist in isolation. It is the newest layer in Mirror Security's platform, which addresses AI risk across the entire lifecycle, from data to model to runtime to identity.
VectaX encrypts inference using fully homomorphic encryption. Embeddings and vector operations stay encrypted end-to-end, so sensitive data never appears in plaintext during model inference. This protects the data plane.
DiscoveR automates red teaming for AI systems. Continuous adversarial testing for prompt injection, jailbreaks, data extraction, and other attack surfaces. This finds the vulnerabilities before attackers do.
AgentIQ provides runtime guardrails for AI workloads. PII detection, hallucination scoring, bias and toxicity analysis, prompt injection defense, and chain security validation, all enforced inline. This protects what the model says and does.
AgentID manages identity and access for autonomous agents. Scoped capability tokens, delegation lineage, runtime policy enforcement, and fast revocation. This controls who the agent is and what it is allowed to touch.
Together, these four layers cover a question that no single product answers alone: How do you let AI agents operate on business-critical systems without losing control of your data, your models, or your access boundaries?
Most organizations today address these concerns piecemeal: a guardrail vendor here, an encryption tool there, identity bolted on as an afterthought. The gaps between those point solutions are where breaches happen. Mirror's platform closes those gaps by design:
VectaX ensures data confidentiality even when third-party models process it
DiscoveR continuously validates that models behave within expected boundaries
AgentIQ enforces content-level safety at runtime
AgentID enforces access-level safety at runtime
The result is a security posture where an agent's data is encrypted, its behavior is guarded, its attack surface is tested, and its access is scoped and auditable. Across every request, every tenant, every agent instance.
Why This Matters Now
Agentic systems are moving from experimentation to business-critical execution. As soon as agents can move money, change records, or access regulated data, the security conversation expands from "is the model safe?" to "is the entire system safe?", covering data, behavior, identity, and access.
Today, security is the single biggest reason enterprises hesitate to deploy autonomous agents into production. Not capability. Not cost. Fear of what happens when an agent touches real systems with real data and real consequences, and something goes wrong.
Mirror Security exists to eliminate that hesitation.
We are building a security harness for the agentic era. A platform where enterprises can deploy and scale autonomous agents with confidence, knowing that data confidentiality, model safety, runtime behavior, and access control are handled by default. Build your agents with any framework, in any language, on any cloud. Mirror wraps the security around them so your engineering teams can focus on capability, not compliance.
The goal is simple: security should never be the reason an organization slows down its AI strategy. When the harness is in place, with data encrypted, models tested, outputs guarded, and access scoped, teams can move fast because the guardrails move with them. Every agent, every tenant, every request.
That is the future we are building toward. AgentID is the latest step, and we are just getting started.